Finally.
Strengthen IEC 62443 Readiness
Without Slowing Development
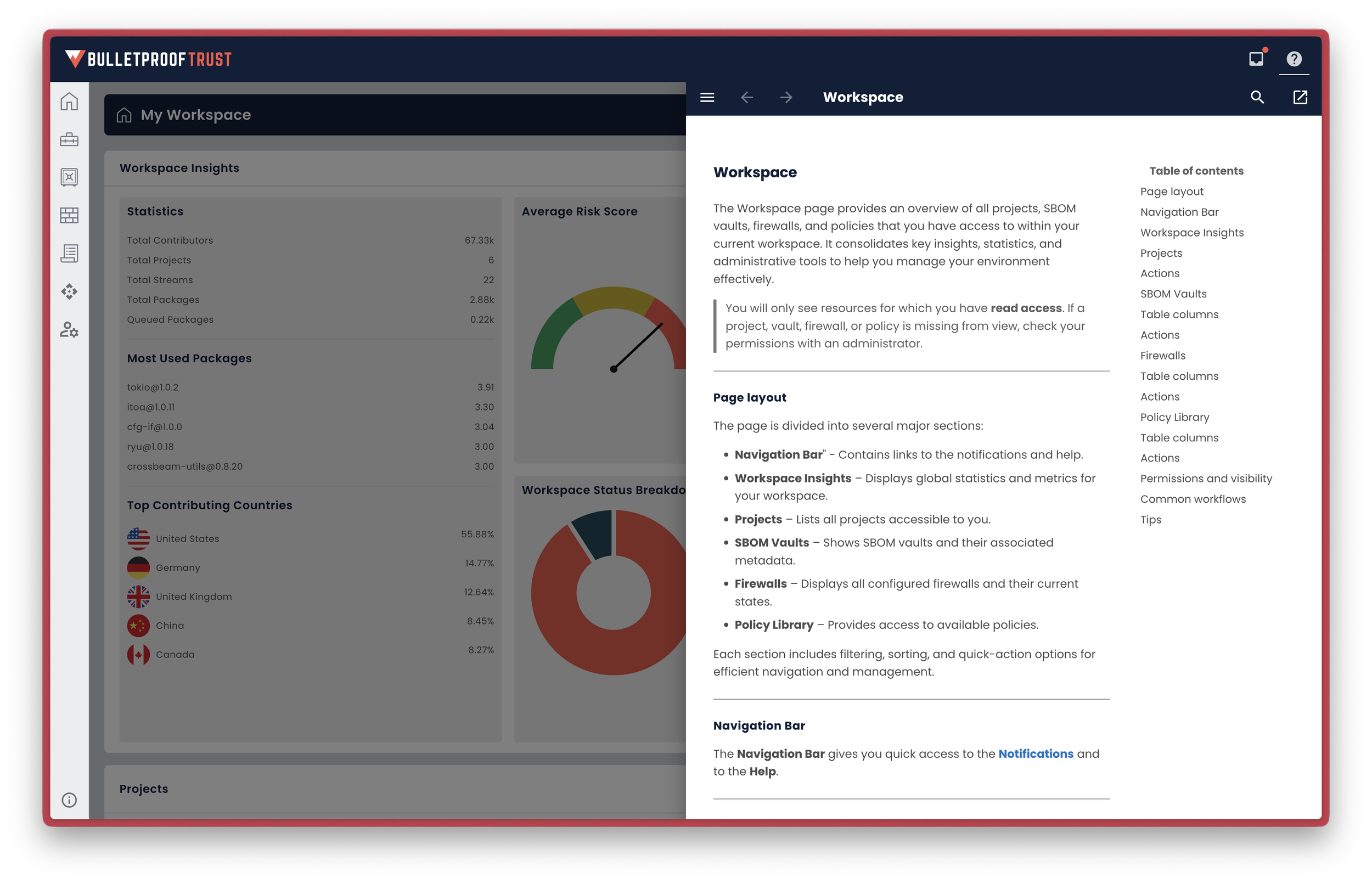
Bulletproof Trust gives product suppliers, system integrators, and asset owners the SBOM management, supplier SBOM intake, contributor intelligence, policy enforcement, and continuous vulnerability monitoring needed to reduce software supply chain risk in industrial and connected products.

Proactive Compliance
Reduced Remediation Costs
Secure-by-Design Device Dev.
Block Non-Compliance Now
Secure SBOM Storage
Compliance Validation Checks
Audit Traceability
CycloneDX / SPDX Generation
3rd Party Software Monitoring
License Risk Identification
Assess Geopolitical Risk
Policy Driven Risk Enforcement
40+ Vulnerability Databases
SBOM Threat Analysis
Automated Risk Comparison
Real-Time Threat Intelligence

Who is this For?
Bulletproof Trust is for product suppliers, system integrators, service providers, and operators in transportation, automotive, rail, aviation, ports, roadways, utilities, manufacturing, water, and other critical infrastructure markets that rely on industrial or connected software.
If you build, integrate, support, or evaluate software-intensive OT components, embedded devices, industrial software applications, or supplier-delivered software for critical systems, Bulletproof Trust helps you understand the software inside your product, where risk is coming from, and how to control it before it reaches development, integration, or operations.
Where we Fit?
Bulletproof Trust is strongest where IEC 62443 requires control over the software inside the product: software inventory, SBOM generation and management, supplier SBOM intake, vulnerability monitoring, contributor and component risk review, policy enforcement, and evidence that software supply chain risk is being managed over time.
It is especially relevant to secure product development lifecycle work and to supplier / integrator evidence needs. It supports component evaluation, procurement, integration, and ongoing risk assessment with better software supply chain visibility and stronger evidence.
How Bulletproof Trust™ Helps
The software supply chain parts of IEC 62443 that Bulletproof Trust can materially improve.
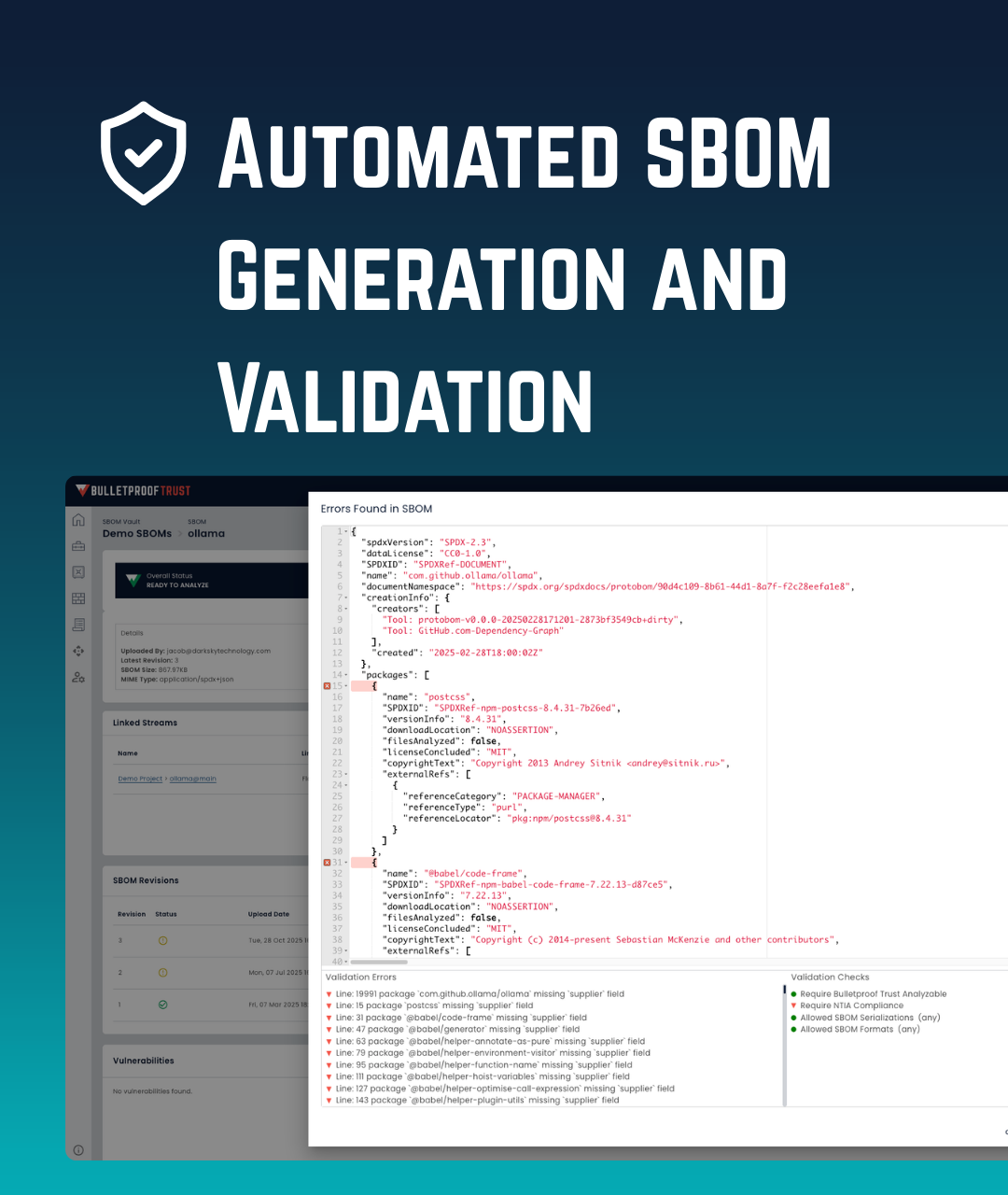
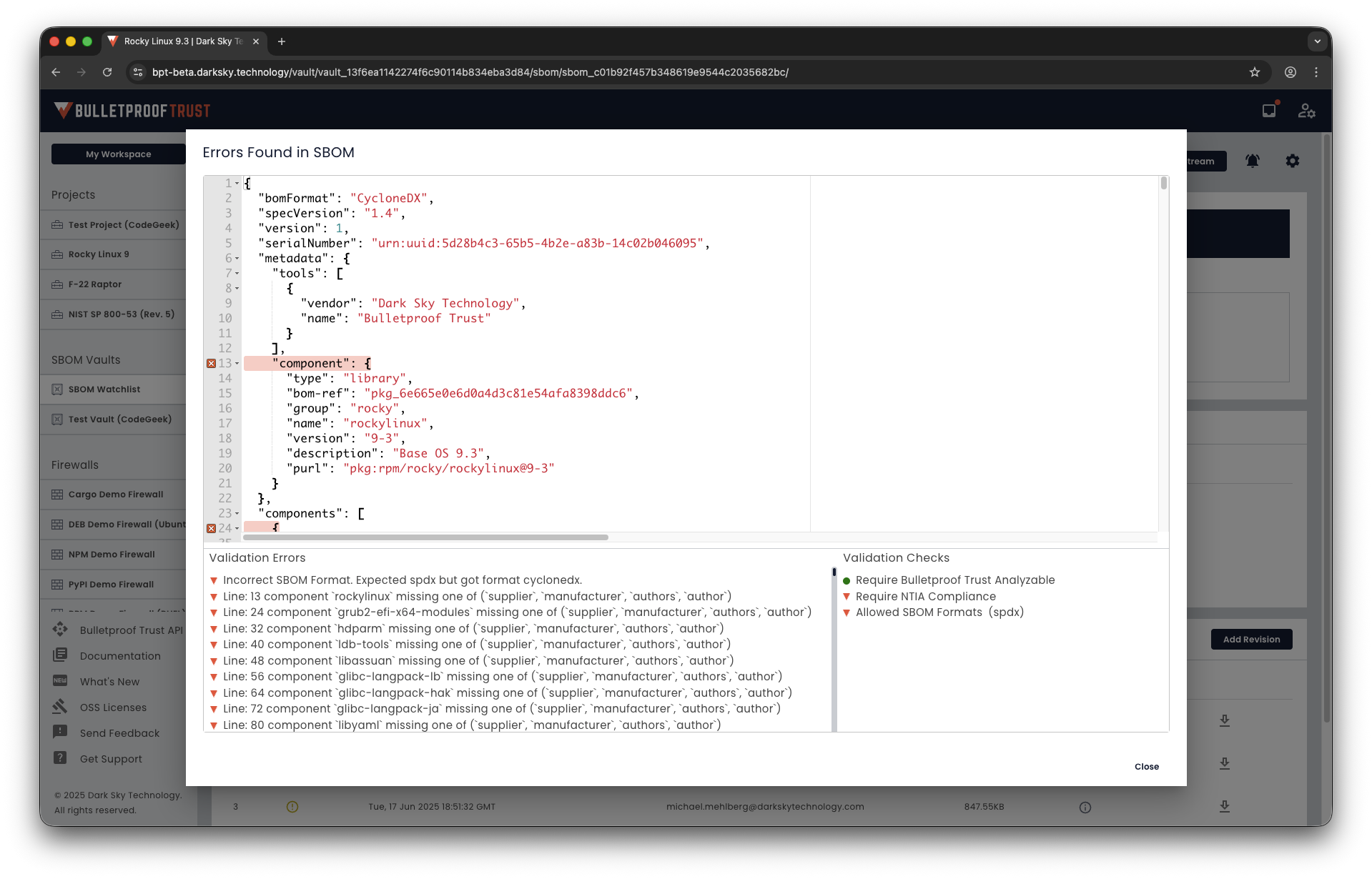
SBOM generation, management, and validation
Generate SBOMs, securely receive supplier SBOMs, store them across projects and programs, validate format and minimum elements, verify contents, and maintain revision control over time.
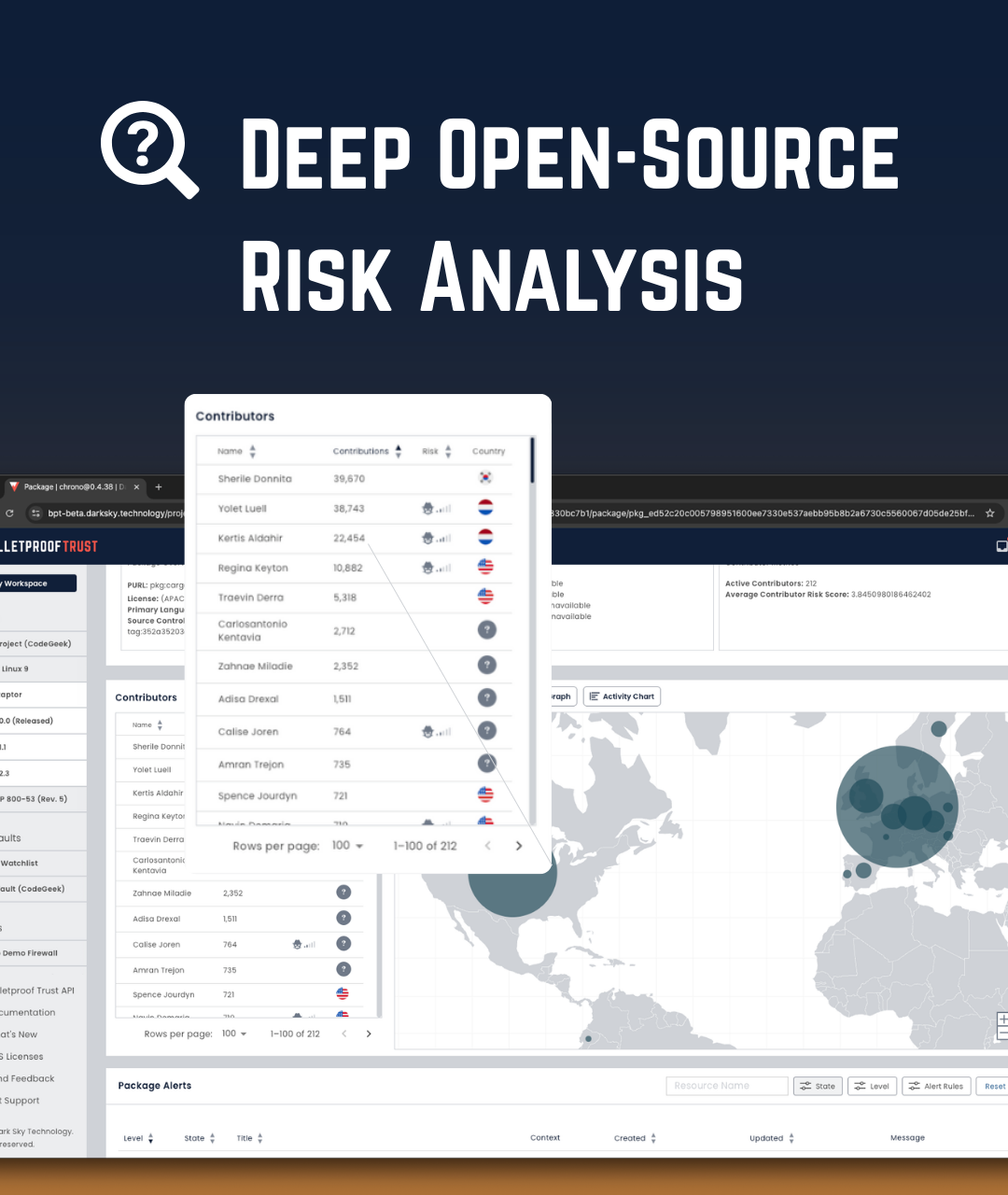
Supplier and contributor trust analysis
Go beyond software composition analysis by evaluating contributor identity, nationality, sanction status, behavioral risk, and geopolitical risk. Detect software linked to sanctioned entities, foreign adversaries, or other untrustworthy actors before it is merged or consumed.
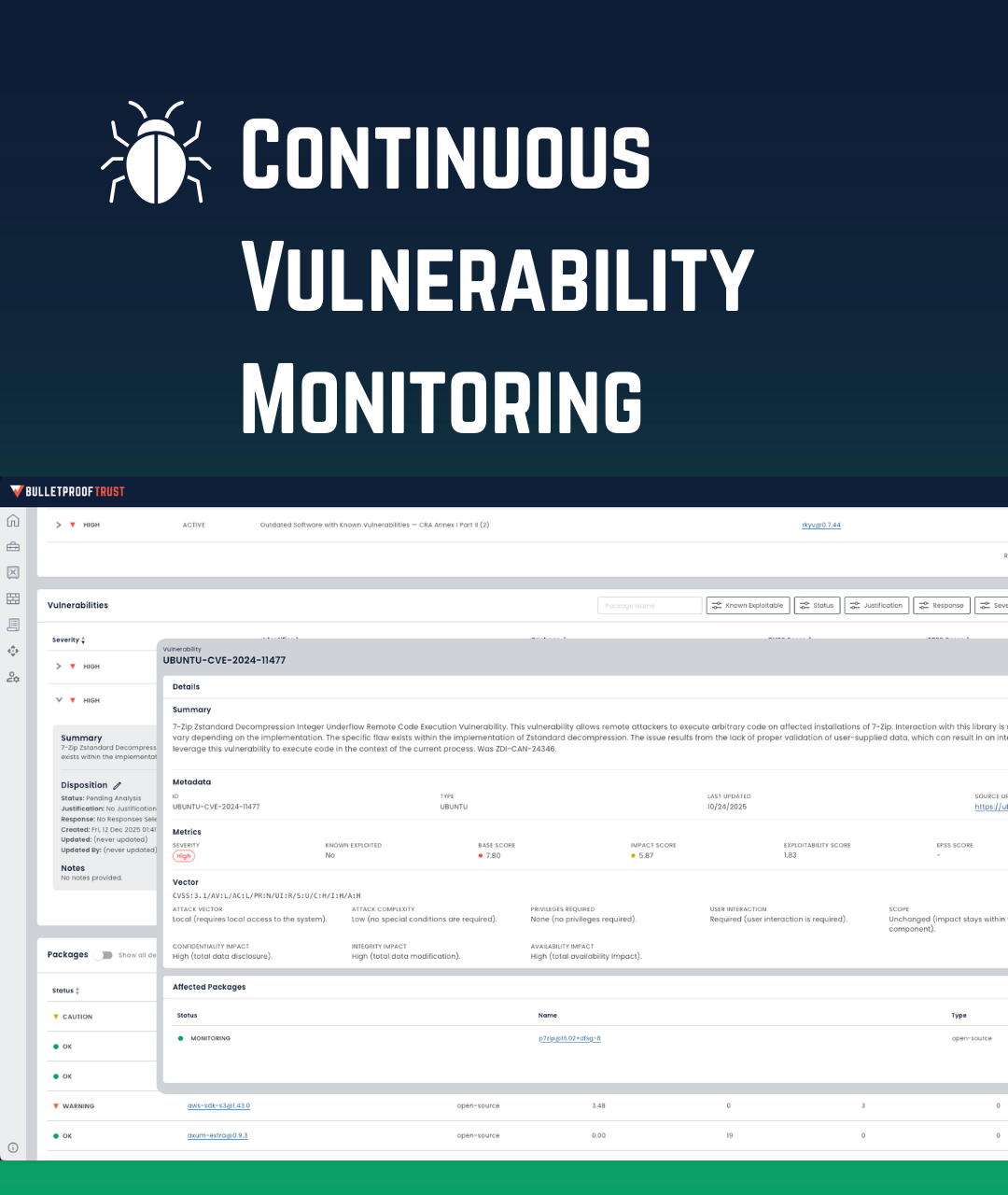
Continuous vulnerability and package-health monitoring
Continuously monitor every package and dependency in your SBOM for vulnerabilities from nearly 40 vulnerability databases, while also identifying deprecation risk, code-quality issues, hidden secrets, copyright problems, and license mismatches.
Policy enforcement before risk enters development
Store pre-canned and custom policies in one place, define the risks that matter to your organization, and block risky contributors, vulnerable packages, and incompatible licenses before they enter the pipeline.
Actionable remediation support
Receive prioritized risk insights, upgrade and downgrade paths, and what-if scenarios so teams can reduce risk quickly instead of just collecting more findings.
High-assurance deployment and integration
Deploy SaaS, private cloud, on-prem, or air-gapped, and integrate through the UI, API, or CLI without exposing sensitive code or environments.

Capabilities that produce IEC-aligned product evidence.
What Bulletproof Trust Delivers
SBOM Vault & management
Encrypted, bit-for-bit SBOM storage with metadata, revision history, NTIA/format interpretation, rich/textual diffs between revisions, and download of exact or augmented copies.
SBOM vendor portal & workflows
Vendor/stakeholder upload and receiver flows, anonymous submission options, folder permissions, and archive/restore semantics for supplier SBOM intake.
Contributor provenance & risk signals
Maintainer/contributor intelligence, provenance mapping, foreign-influence/FOCI flags and policy-driven contributor alerts to support supplier trust decisions.
Streams, baselines & revision comparison
Create Streams from SBOMs, pin or lock stream revisions as a product baseline, and produce diffs and reports that demonstrate approved changes over time.
Continuous vulnerability monitoring & prioritization
Ongoing monitoring of vulnerability sources and package-health metrics with prioritized alerts and remediation timelines suitable for post-market review and authorization evidence.
Policy templates & Annex mappings
Pre-mapped controls to IEC/NIST (Annex-style), plus downloadable evidence packs that tie artifacts to product-level clauses customers must show.
Air-gapped / on-prem options
Full functionality for disconnected environments with encrypted storage and restricted access models.

What You Can Prove with Bulletproof Trust
Walk away with these auditable outcomes.


SBOM Validation and Verification
Bulletproof Trust shows you and your auditors whether an SBOM was generated, received, validated, and stored correctly.


3rd Party Components and Dependencies
Bulletproof Trust shows you and your auditors what 3rd party components and dependencies are inside your product. Every detail revealed.
Continuous Supply Chain Monitoring
Bulletproof Trust never stops monitoring your software supply chain. You get point-in-time evidence with continuous analysis long after deployment.
Risk Illumination
Bulletproof Trust shows you which packages, contributors, vulnerable packages, or incompatible licenses are risky for your deployments.

Trusted by national critical systems, and deployable in sensitive air-gapped environments.
Built originally to protect stringent defense systems, now securing IEC 62443 regulated technologies.
Designed for Regulated Environments

Your code is sensitive, and you can’t share it with anyone. Bulletproof Trust can deploy in air-gapped environments, so you don’t have to share anything with us.
Deploy Air-Gapped

Personally identifiable information (PII) comes with a whole separate set of rules, regulations, and laws. Bulletproof Trust masks every bit of data so you never have to handle PII.
Avoid Dealing with PII
Connect directly to the API to perform all analysis, manage the platform, and integrate with your build environment. Or, drive Bulletproof Trust from the command-line with included CLI tools.
API First, CLI Enabled


Bulletproof Trust has been assessed and found awardable by the Chief Digital and Artificial Intelligence (CDAO) office and the Air Force Platform One Marketplace team.
Trusted by our Best Agencies
TRL9
Bulletproof Trust is Technology Readiness Level 9 (TRL9), deployed by government entities and commercial enterprises in SaaS, on-prem, private-cloud, and air-gapped environments.
Deployed and Battle Tested

Bulletproof Trust integrates with artificial intelligence large language models (AI LLM) through the Model Context Protocol (MCP). Get answers and deep insights on your risk data.
AI LLM Integrated

Bulletproof Trust is a 100% US owned and operated company developed by 100% US citizens, cleared or clearable.
Made in the USA

No complex calculations. No API call or user tracking. Our pricing is transparent, simple to understand, scalable across the smallest projects to the largest enterprises.
Transparent Pricing